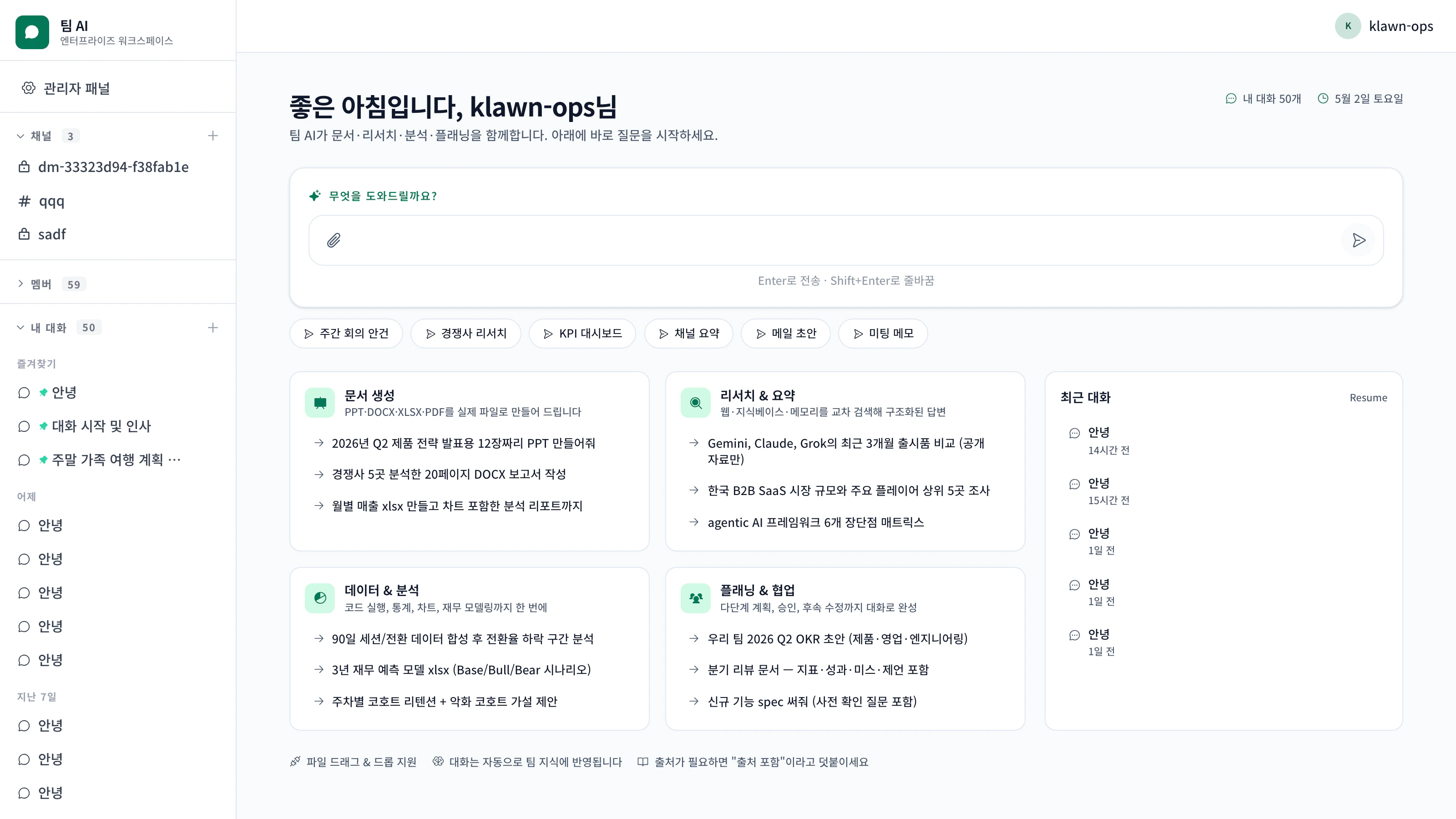
Teeem AI leaves your existing systems in place and connects only the information and execution flow. No new ERP, no data migration. When an employee asks for something in plain language from the messenger they already use, the following six steps unfold inside a single response.Documentation Index
Fetch the complete documentation index at: https://docs.teeem-ai.com/llms.txt
Use this file to discover all available pages before exploring further.
The six-step flow
Entry — request from where the team already works
Slack mentions, KakaoTalk group rooms, web chat, Microsoft Teams, REST calls from internal portals. No new tool to learn.Teeem AI identifies the channel, verifies the sender, and forwards the request to the next step.
Context — pull scattered company data into the question
Information needed to answer is gathered from across your systems.
- Knowledge base — internal docs, policies, report templates
- ERP / groupware — Douzone or Wehago for invoices, accounts, approvals
- Email / calendar — the employee’s own Google or MS365 (via OAuth)
- E-commerce — Cafe24, Naver Smartstore orders and inventory
- Internal apps — App Pack models (orders, inventory, tasks, etc.)
- Conversation history — earlier context in the same channel or thread
Insight — surface the change points
Not just a list of data — Teeem AI surfaces the meaningful change points.Example: “Last week’s revenue was ₩120M, −15% vs the prior week. The biggest impact was account A (−₩30M). Likely cause: shipping delay.”Tools commonly used at this step:
- Time-series analysis (
forecast) - Threshold monitoring (
alert_monitor) - Document comparison (
diff_documents) - Data analysis (
analyze_data)
Trust layer — protect sensitive data and stay within permissions
Before a response is composed, the following checks run:
The masked PII is restored exactly before the response goes back to the user.
| Check | Behaviour |
|---|---|
| PII masking | 10 Korean PII types auto-masked before reaching the LLM |
| Permission check | RBAC + ABAC verify the sender can access the requested data |
| Prompt-injection defence | Hidden injection attempts in external content (email, web, docs) are blocked |
| Output leak detection | Responses are monitored for PII or secrets escaping |
| Approval gates | Sensitive actions (external sends, payments, bulk downloads) require human approval |
Systems — connect to existing systems instead of replacing them
Beyond the answer, the agent acts — but only when permissions allow.
- Generate a sales report PPTX/PDF and attach it to a Slack channel
- Draft a quotation in HWP and email it to the account (with approval)
- Export tax invoices from Douzone to Excel
- Create a calendar event with a Meet link
- Add a record to an internal app (e.g. order management)
Records — audit log of who did what for whom
Every step is recorded in a tamper-evident hash-chain audit log.
- Who requested what
- Which data was accessed
- Which permission checks ran
- Which tools were called and what they returned
- What response went out (with PII masking statistics)
GET /admin/compliance-report exports the entire record as a single ZIP — suitable for direct submission during regulatory audits or ISMS-P recertification.At a glance
Three guiding principles
Systems stay in place
No replacements. Existing ERP, groupware, internal systems are connected, not swapped.
Inside permissions only
Data access, tool execution, external sends — all gated by the sender’s permissions.
Recorded without gaps
Every action is logged tamper-evidently. Five years of retention.
Next
Agentic workflow inside one response
See the same six steps unfold within a single message, in detail.
Permission model deep-dive
How RBAC + ABAC + IP allowlist + tool gates combine.